Simplifying MCP server authentication for enterprises
See how MCP authentication is messy today and how a unified approach makes servers secure, discoverable, and manageable.
Model Context Protocol (MCP) is quickly becoming the standard way to connect AI agents with the tools and data they need. In principle, it looks simple: spin up an MCP server, point your agent to it, and you’re ready to go.
But as soon as teams move from a demo to production, a major friction point shows up — authentication. Every MCP server expects its own method of proving identity. Some rely on API keys, others use OAuth, and many leave authentication up to developers to implement themselves.
What feels straightforward with one server becomes a headache when you’re running dozens across your organization.
The authentication problem in MCP servers
Unlike protocols that ship with a standardized security model, MCP leaves authentication as an open question. That flexibility helps experimentation, but it creates real challenges once multiple servers are in play.
- No built-in standard: The spec doesn’t enforce a consistent way to handle authentication. Every server author decides independently — some use API keys, some implement OAuth, others offer no authentication at all.
- Every server becomes its own identity provider: Each server must issue, validate, and manage tokens on its own. In effect, every MCP server operates as a mini identity provider (IdP). This adds unnecessary complexity for developers and inconsistency for enterprises.
- Credential sprawl
With every server requiring its own keys or tokens, teams quickly accumulate dozens of credentials to distribute, rotate, and revoke. The operational burden grows linearly with the number of servers. - Agents can’t “log in”: OAuth flows are designed for humans, not LLMs. While a user can click through a redirect and approve access, an agent can’t. This leaves developers either weakening security (hardcoding keys) or building extra orchestration layers to manage credentials on behalf of agents.
- Governance gaps: Without centralized authentication, enforcing role-based access, setting budgets, or ensuring compliance becomes fragmented. Each server has its own rules, and enterprises are left without a single point of control.
Why this matters more at enterprise scale
For a single MCP server, the authentication overhead might feel manageable. You set up one API key or walk through one OAuth flow, and the friction is tolerable. But enterprises rarely stop at one server.
In practice, organizations quickly spin up dozens or even hundreds of MCP servers: connecting internal databases, SaaS apps, research tools, and custom workflows. At this point, the lack of a unified authentication model turns into a major roadblock.
- Operational overhead multiplies: Every new server introduces another set of tokens, credentials, and permissions to track. Rotating keys or revoking access means repeating the process across all servers.
- Security risks grow: With more servers comes more potential for mistakes. Hardcoded tokens, forgotten credentials, or inconsistent access policies increase the risk of leaks and unauthorized use.
- Shadow MCP servers appear: Developers often stand up new servers informally to test ideas. Without centralized authentication, these servers may operate outside of enterprise security policies, creating blind spots.
- Adoption slows down: Even when the technical integration is simple, the authentication hassle discourages teams from adding more MCP servers. What should be a flexible, composable ecosystem instead becomes fragmented and hard to scale.
What a better approach looks like
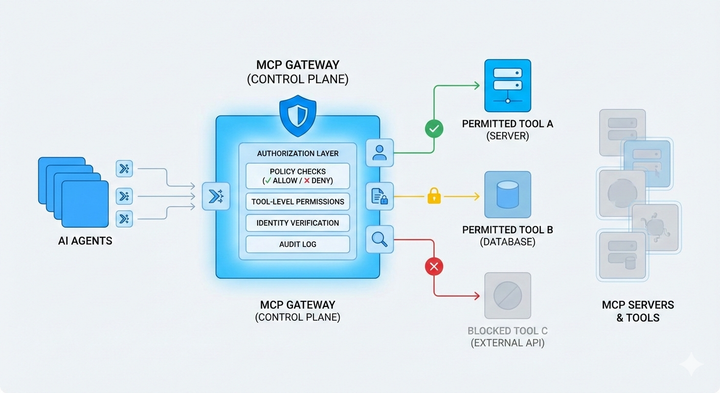
Enterprises need an authentication model that scales with the number of MCP servers, instead of multiplying the burden with each one. That means shifting from server-by-server credentials to a single, unified layer of authentication and access control.
A better approach has a few key qualities:
- Users and agents should only have to authenticate once. That identity should carry across all MCP servers, without requiring separate tokens or logins for each.
- Permissions and limits need to be defined in one place, then applied consistently across all servers. This ensures governance and compliance don’t depend on ad hoc server-level rules.
- Instead of custom implementations, OAuth should be provided out of the box. Developers shouldn’t have to rebuild secure login flows for every server they deploy.
- Tokens and credentials must be provisioned in a way that LLM agents can actually use. That means secure, non-interactive flows designed for machines, not humans clicking through approval screens.
With these foundations in place, MCP can move from a fragmented collection of servers to a coherent, enterprise-ready ecosystem.
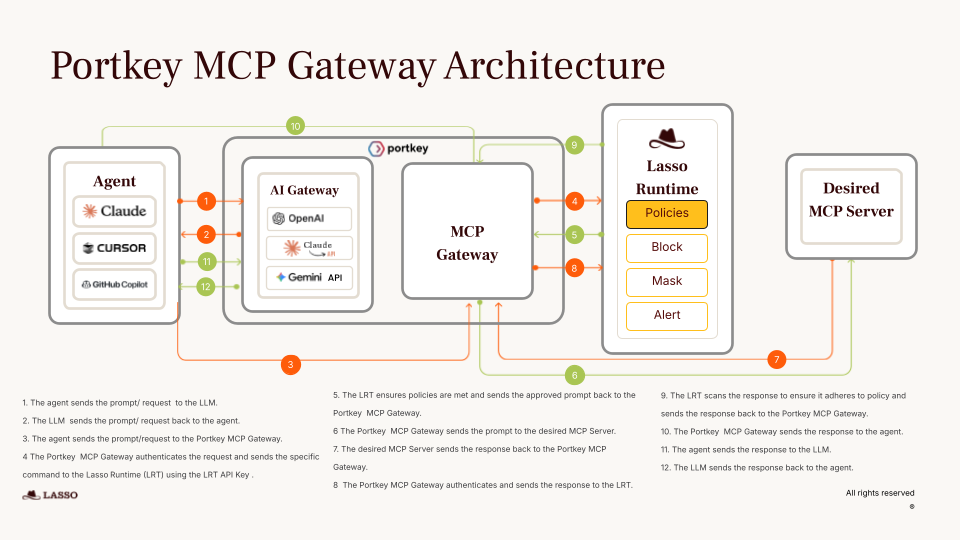
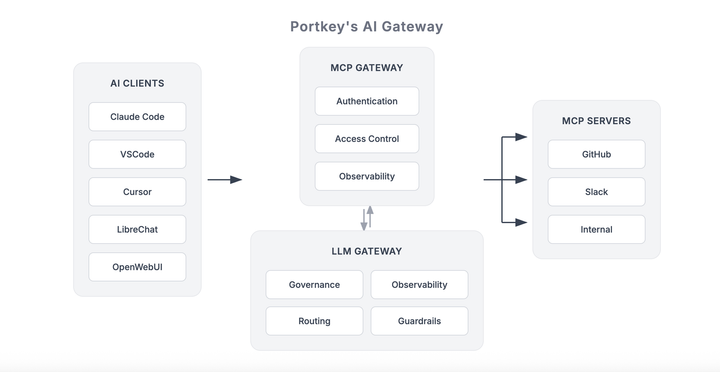
How Portkey solves it
Portkey provides the missing layer of authentication and governance that MCP needs to work in production. Instead of handling logins, tokens, and policies for every server individually, enterprises authenticate once through Portkey and extend that secure access to all MCP servers.
- Unified authentication: With built-in OAuth, Portkey removes the hassle of server-by-server authentication. A single secure connection gives users and agents access to every MCP tool.
- Centralized governance: Role-based access, budgets, and rate limits are applied consistently across servers. Policies are managed in one place, making compliance and audits straightforward.
- Agent-ready flows: Portkey provisions credentials in a way agents can use safely, without weakening security or requiring workarounds.
- Full observability: Every model call, tool invocation, and server interaction is logged. Enterprises get complete visibility into usage, performance, and costs across their MCP ecosystem.
With Portkey, MCP servers stop being scattered, hard-to-manage endpoints. They become secure, discoverable, and manageable infrastructure that teams can build on confidently.
Authentication: the unlock for MCP at scale
MCP is already proving itself as a powerful way to connect agents with the tools and data they need. But without fixing authentication, enterprises will continue to face fragmented access, inconsistent policies, and mounting operational overhead.
A unified authentication layer turns MCP from a promising demo into reliable infrastructure. With Portkey, organizations can connect once, govern access centrally, and monitor usage across every server.
Authentication may look like a small detail, but at enterprise scale, it’s the foundation that makes MCP servers secure, discoverable, and manageable.
👉 Book a demo to see how Portkey simplifies MCP authentication at scale.